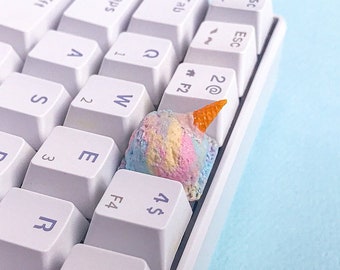
Price: $8.08
Original Price: $8.98
Sale ends in 6 days
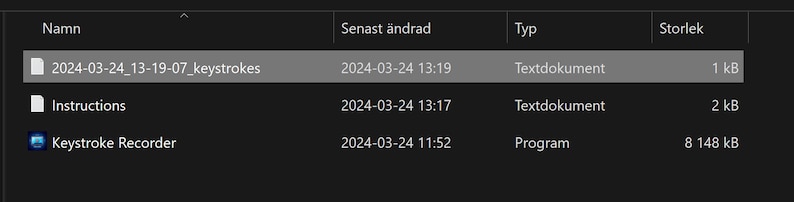
Keystroke Recorder
You can only make an offer when buying a single item
Instant Download
Your files will be available to download once payment is confirmed. Here's how.
Instant download items don’t accept returns, exchanges or cancellations. Please contact the seller about any problems with your order.
Etsy Purchase Protection: Shop confidently on Etsy knowing if something goes wrong with an order, we've got your back for all eligible purchases — see program terms
Captcha failed to load. Try using a different browser or disabling ad blockers.
Other reviews from this shop
|
(102)
Seller was great but never received order 2 times got lost in transit !
David Fimiano Jul 14, 2023
Never received the item. Notified seller was immediately refunded. Thank you!
Jane Braddock Apr 7, 2023
Quality product, corresponds to the description but unfortunately made me detach the sensor
Fatima-sara Aug 23, 2023
Photos from reviews
More from this shop
Browse by section



Disclaimer: Etsy assumes no responsibility for the accuracy, labeling, or content of sellers' listings and products. Electrical or electronic products may pose a risk of fire or electrocution. Vintage, handmade, refurbished, or modified electrical or electronic products may not meet current safety standards and may not be in safe working order. Inspect carefully before use and message the seller if you have concerns relating to the product. Do not use a vintage electrical or electronic item if its safety cannot be verified. To reduce the risk of fire, never leave vintage electrical or electronic products plugged in unattended. See Etsy's Terms of Use for more information.